
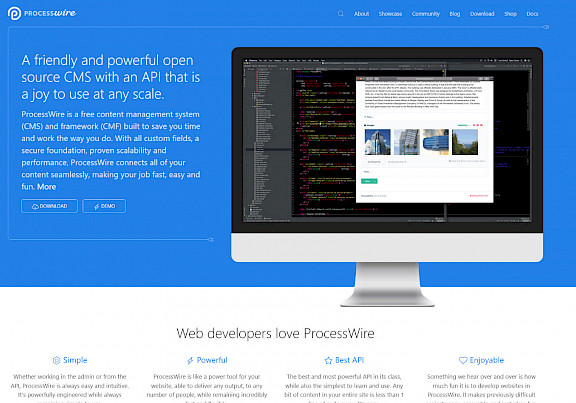
ProcessWire - The CMS that does it all
Using the right tools for the job is at the heart of everything we do - ProcessWire allows us to deliver complex web projects without making compromises
We've been using a lesser-known Content Management System (CMS) called ProcessWire as the foundation for our websites and web applications since 2012.
Whilst you may not have heard of it before, we rate it much more highly than the "big players" - Wordpress, Joomla, and Drupal - for these three reasons:
- Security
- Flexibility
- Usability
Security
ProcessWire is built on a rock-solid codebase, utilising best practices and incorporating the latest standards to ensure it remains as stable and up-to-date as possible.
Unlike many of its competitors, it can also perform the vast majority of tasks required of it out of the box. This means fewer add-on modules and less code for us to audit and keep updated for your web projects.
Since we adopted ProcessWire as our main web development tool back in 2012, we've had zero security issues and none of the usual headaches with applying security updates that we've seen with other systems.
Read our in-depth CMS security article
Flexibility
ProcessWire lends itself to websites of any scale, featuring powerful caching and optimisation tools to ensure your site loads as quickly as possible.
Beyond websites, it can also be adapted for many other uses - we've built booking systems, bespoke CRM applications, online stores and more - it really is a versatile tool.
Read our in-depth CMS flexibility article
Usability
All of this comes with an extremely customisable user interface as well. Out of the box, we can configure each section to be simple for you to manage any content you with to, whether it's writing an article, managing an image gallery, publishing content on a schedule - everything can be laid out simply and efficiently.
We've had many customers complement us on how easy and enjoyable the system is to use and that is testament to the amount of thought and care that has gone into the software even before we begin customising it for your project.
Leave a comment